- 0.1 Home
- 0.2 About Us
-
0.3 Products
-
0.0 Software
- 0.0 Speech Recog.
-
0.0 PDF Solution
-
0.0 For Windows
- 0.0 Kofax Power PDF
- 0.0 Xodo PDF Studio for Windows
- 0.0 For Macintosh
- 0.0 For Linux
-
0.0 For Windows
- 0.0 LiquidText
- 0.0 OCR
- 0.0 Document Manag.
- 0.0 E-sign
- 0.0 Point of Sale (POS) System - 815J
- 0.0 Dicom Viewer
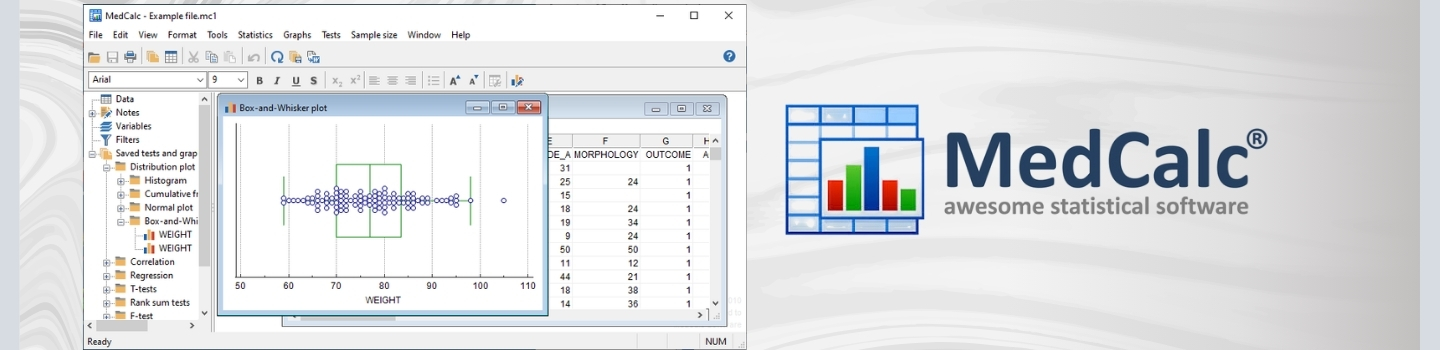
- 0.0 Medical Statistical Software
- 0.0 iManage document management
-
0.0 Hardware
- 0.0 Microphone
- 0.0 Digital Voice Recorder
- 0.0 Istorage Hard Drives
- 0.0 Portable Meeting Recorders
- 0.0 GPS Clock
- 0.0 POS
- 0.0 Healthcare Display
- 0.0 Document Visualizer
-
0.0 Software
- 0.4 Partners
- 0.5 Clients
- 0.6 Support
- 0.7 Careers
- 0.8 Contact Us
ICONS INFOCOM PVT. LTD.
ICONS Infocom Pvt. Ltd. is an experienced and trusted IT distributor and reseller headquartered in Mumbai with a strong Pan-India presence. The company is certified with ISO 9001:2015, ISO 27001:2022, and ISO/IEC 20000-1:2018, demonstrating our commitment to quality management, information security, and internationally recognized IT service management standards.
At ICONS Infocom, we are an authorized provider of leading speech recognition, document management, and productivity solutions designed to help professionals, enterprises, healthcare institutions, and organizations streamline documentation, automate workflows, and improve operational efficiency.
Our dedicated team supports clients across India with genuine licensed software, expert consultation, and dependable technical support. By working closely with globally recognized technology partners, we ensure customers receive authentic products, compliant licensing, and long-term service support.
https://mail.iconsinfocom.com/images/mod_jbgmusic/ICONS/ICONS-Corp-Music.mp3
!{!164346632,192034629,203021853
Overview
Why choose diskG*?
 Did you know that tens of millions of external data storage devices are lost every year and this figure is rising. Have you ever considered the impact of losing your non-encrypted hard drive or USB flash memory key? Your data would be at the mercy of anyone who stumbles across it. Your personal videos may appear on YouTube, your business data sent to a competitor, your personal and financial information used for fraudulent purposes.The Information Commissioner’s Office (ICO) now has the power to fine businesses and government bodies up to £500,000 for serious breaches of the Data Protection Act. This includes the loss of an unencrypted portable hard drive or USB flash memory key that contains customer data. The ICO has been very clear in advising businesses to encrypt all data that workers access, they also recognise that data which is encrypted and lost or stolen is not vulnerable to compromise.Loss of confidential data can have a devastating effect on both businesses and consumers. It could lead to a hefty fine, the downfall of a business, embarrassment, job losses and adverse media focus. The diskG* can protect you against all of this.
Did you know that tens of millions of external data storage devices are lost every year and this figure is rising. Have you ever considered the impact of losing your non-encrypted hard drive or USB flash memory key? Your data would be at the mercy of anyone who stumbles across it. Your personal videos may appear on YouTube, your business data sent to a competitor, your personal and financial information used for fraudulent purposes.The Information Commissioner’s Office (ICO) now has the power to fine businesses and government bodies up to £500,000 for serious breaches of the Data Protection Act. This includes the loss of an unencrypted portable hard drive or USB flash memory key that contains customer data. The ICO has been very clear in advising businesses to encrypt all data that workers access, they also recognise that data which is encrypted and lost or stolen is not vulnerable to compromise.Loss of confidential data can have a devastating effect on both businesses and consumers. It could lead to a hefty fine, the downfall of a business, embarrassment, job losses and adverse media focus. The diskG* can protect you against all of this.
How does it work?
Step 1 - Plug integrated USB2 cable in to any PC, MAC or Linux system
Step 2 - Enter your personal 6-16 digit PIN on the alphanumeric keypad
Step 3 - You're up and running
Once access to the diskG* is granted by entering the correct 6-16 digit PIN, data can be copied to the diskG* using any off the shelf backup software, or simply drag and drop files and directories using Windows Explorer. Once the diskG* is disconnected, all data is encrypted and cannot be accessed unless the correct PIN is entered.
Military strength Hardware encryption
The encryption chipset incorporated within the diskG* encrypts all data using 128-bit or 256-bit AES Hardware Encryption. The diskG* is the only USB hard drive to be awarded the CESG CCTM government accreditation. The diskG* also utilises FIPS PUB 197 validated Encryption Algorithm.
The recommended standard for symmetric encryption is AES (advanced Encryption Standard). The Committee of National Security Systems (CNSS) rates the AES algorithm as acceptable for encrypting top secret data on their AES policy fact sheet, stating “The design and strength of all key lengths of the AES algorithm (i.e. 128,192 and 256) are sufficient to protect classified information up to the SECRET level. TOP Secret information will require use of either the 192 or 256 key lengths.”
Brute Force Hack Defence Mechanism
The diskG* uses a three pronged approach to protect against a Brute Force Attack. The first step is to deny access to the drive until the drive can verify the user PIN. After six incorrect attempts the drive will lock itself, requiring the drive to be disconnected and then reconnected. This feature blocks automated attempts to enter PIN numbers. Lastly, after one hundred incorrect PIN attempts, the diskG* assumes it is being attacked and will destroy the encryption key and lock itself, rendering the data useless and requiring a total reset and reformat to redeploy the diskG*.
VTC Technology
The diskG* also incorporates Variable Time Circuit (VTC) technology, which thwarts “timing attacks” aimed at accessing the drive by studying the behaviour and infiltrating diskG*’s electronics.
What is the difference between software and hardware encryption?
Software encryption:
- Complex passwords can be cracked easily and quickly with a Brute Force Attack
- Simple password cracking software is readily available on the internet, often free of charge
- Software encryption is vulnerable to key loggers – where every key pressed is logged in either a software or hardware key logger
- Software encryption can be corrupted by viruses
- Software encryption is much slower when compared to hardware encryption
- Software encryption needs to be installed on each computer that the external storage device is used on
Hardware encryption:
- The diskG* cannot be brute force attacked
- The diskG* is not vulnerable to keyloggers as the PIN is entered on the unit rather than the keyboard
- The diskG* is not vulnerable to malware or viruses
- Encryption is performed in real-time thus there is no speed degradation
- No software or drivers are required
Technology Partner
Icons Infocom | Speech Recognition | Voice Recognition | Dragon Naturally Speaking | Dragon Medical | Dragon Legal | Dragon Professional Individual | Power PDF | Andrea Microphones | Wireless Microphones | Wired Microphones | Array Microphones | Istorage Devices | Speech Recognition India | Tungsten PDF | iManage | Liquidtext | Elmo Document Visualizer | Numeric UPS | Barco Montiors | RadiAnt | MedCalc
Copyright © 2014 Icons Infocom
Designed & Developed By Iconsdigital.in